
Risk Lives In The Gaps
Dismantle the Hidden Attack Chains that Traditional Scanners Can't See
Introducing LARCK

| Linked Asset Risk Capability Knowledgebase |
LARCK Identifies risky software capability overlaps traditional tools don’t prioritize.
Software Capability Mapping
Capability Overlap Detection
Explainable Risk Scoring
Prioritized Action Signals

Our Perspective
Capability Creates Risk - Even Without Exploits
Most security and IT tools focus on: known vulnerabilities, active compromise, and detected anomalies. These signals are important, but they are inherently reactive.
LARCK takes a different approach.
Instead of starting with incidents, LARCK evaluates the capabilities enabled by the software running on each endpoint. By understanding what tools can do — and how those capabilities overlap — LARCK identifies risk that exists before exploitation, alerts, or abnormal behavior occur.
This perspective shifts risk management from detection to prioritization, helping teams focus on the endpoints that matter most — even when nothing appears “wrong” yet.

Introducing LARCK
Linked Asset Intelligence
Connect assets, software, identities, and operational context into a unified knowledge graph, revealing relationships that traditional inventories miss.
Continuous Knowledge Engine
LARCK continuously ingests discovery, integrations, and operational signals to keep asset intelligence current — not snapshot-based.
Risk Chain Modeling
Identify how combinations of software, services, and configurations create chained exposure paths
Stop Counting Assets. Start Understanding Them.


Utilize integrated dashboards that correlate asset inventory, installed software, and behavioral risk patterns to surface true endpoint exposure—across the entire environment and down to individual systems.
Operationally Actionable Output
Turn asset intelligence into workflows, prioritization signals, and automation triggers — not passive dashboards.

A single, unified view that shows why an endpoint is risky—not just that it is. LARCK correlates installed software, capability categories, and multi-software risk patterns to surface true exposure, prioritize action, and explain risk in plain terms.

Stop Chasing CVE's and Start Breaking Chains to Reduce Your Attack Surface
Traditional tools show you isolated vulnerabilities in a vacuum. LARCK reveals the Attack Vector Chain. We map how an attacker leverages a minor configuration "gap" to gain a foothold, escalate privileges via software capabilities, and move laterally toward full environment compromise.
By understanding these interdependencies, you can break the entire chain by removing a single strategic link. This turns remediation from an endless game of "patch-a-mole" into a surgical strike against an attacker's path.

Intelligent Vulnerability Management
Just Because a Vulnerability is Critical, Doesn't Mean it's at the Top of the List in Your Environment.
CVSS, SVCC, EPSS, KEV... each of them say that you shouldn't rely on their score alone in determining what is truly top priority in your environment. Often times, a 'High' severity vulnerability is is more dangerous for your company than a 'Critical' one. LARCK takes all methodologies into account to provide accurate, clear, and concise remediation recommendations for you to increase your security posture.
Know Exactly What You Need to Remediate at a Glance.

Turn Normal Vulnerability Lists:
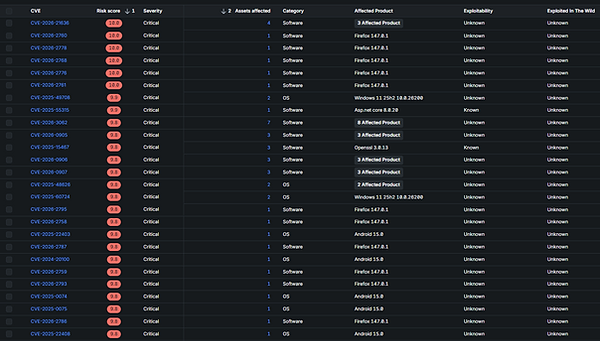
Into Industry Standard, Guided Remediation Tasks:

See the top vulnerable software to patch, along with organized, prioritized tasks that follow standard methodologies, like SVCC seen above.
Simplified, Dynamic Microsoft Windows Update Reports

Make 'Patch Tuesday' simple with a guided Cumulative Update Dashboard, which shows you what is installed, and what needs to be installed.. ensuring that you are current, timely, and compliant.
